mirror of
https://github.com/fatedier/frp.git
synced 2026-05-15 16:15:49 -06:00
[GH-ISSUE #4168] x-forwarded-proto gets stripped away in http proxies #3283
Labels
No labels
In Progress
WIP
WaitingForInfo
bug
doc
duplicate
easy
enhancement
future
help wanted
invalid
lifecycle/stale
need-issue-template
need-usage-help
no plan
proposal
pull-request
question
todo
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference: github-starred/frp#3283
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @panta82 on GitHub (Apr 17, 2024).
Original GitHub issue: https://github.com/fatedier/frp/issues/4168
Bug Description
I'm using setup:
nginx[443] (SSL termination) -> proxy_pass[http] -> frps[http] -> ...tunnel... -> frpc[http] -> local service[http]This works, however on the other side,
X-Forwarded-Protoheader gets changed, which creates problems for cookies (the app thinks it's not behind HTTPS, which is incorrect).Here's the diff:
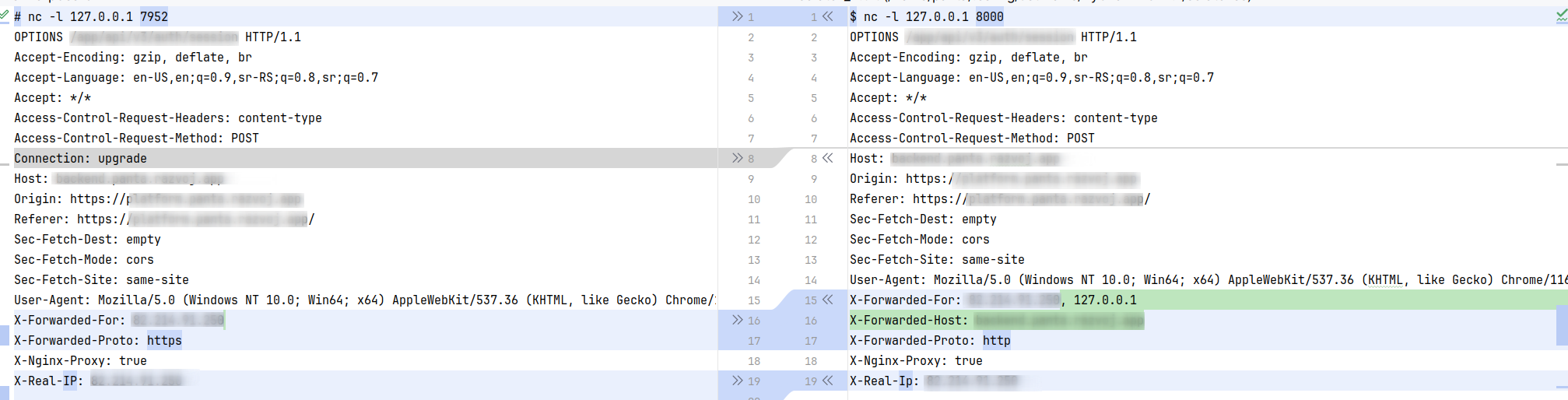
Left side: What is sent from nginx to frps
Right side: What is sent from frpc to the client
Frps adds
X-Forwarded-Host(good), but changesX-Forwarded-Protofromhttpstohttp.frpc Version
0.57.0
frps Version
0.57.0
System Architecture
linux/amd64
Configurations
frps.toml:
frpc.toml:
client.example.com.conf (nginx):
Logs
No response
Steps to reproduce
???
Affected area
@fatedier commented on GitHub (Apr 18, 2024):
This should be expected, otherwise the client can pass any untrusted content.
In your scenario, you can test whether the issue can be resolved by using
requestHeaders.set.x-forwarded-proto = "https".@panta82 commented on GitHub (Apr 18, 2024):
Understood. I can certainly hack it in.
It might be useful though for frps to have some kind of "behind proxy" mode, where this header is trusted. Because I assume this will be a 99% use case for the tool.
(also, should
x-real-ipthen be passed through?)@fatedier commented on GitHub (Apr 18, 2024):
More about the configuration of the 7th layer HTTP will be planned for the future v2 version, and currently, no additional configuration options will be provided.
x-real-ipis not a standard header defined by the RFC. The current code uses the native handling logic of Go and does not perform any additional processing.@panta82 commented on GitHub (Apr 18, 2024):
Ok, that's fair. Closing the issue.