mirror of
https://github.com/fatedier/frp.git
synced 2026-05-15 08:05:49 -06:00
[GH-ISSUE #2831] Cant connect with tcp over tls, but non-tls tcp works #2263
Labels
No labels
In Progress
WIP
WaitingForInfo
bug
doc
duplicate
easy
enhancement
future
help wanted
invalid
lifecycle/stale
need-issue-template
need-usage-help
no plan
proposal
pull-request
question
todo
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference: github-starred/frp#2263
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @presidenten on GitHub (Mar 10, 2022).
Original GitHub issue: https://github.com/fatedier/frp/issues/2831
Bug Description
tl;dr
What I did
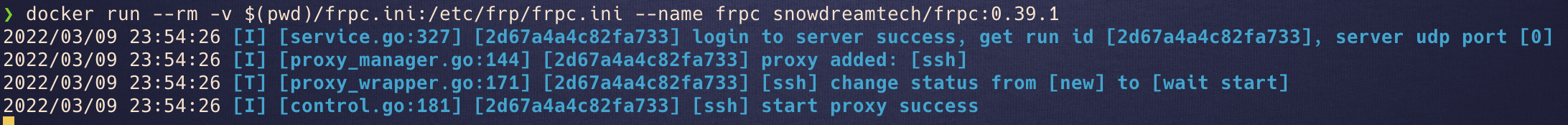
I expose server through ingress with tcp - works
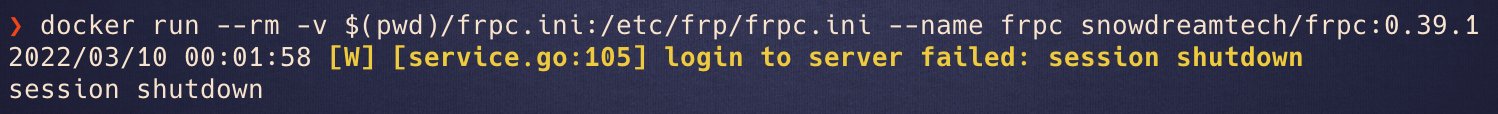
I expose server through ingress with tcp over tls and same port -
login to server failed: session shutdownWhat I expected to happen
I expected frp to connect like normal
Long version of setup and what I tried to verify that all parts are working
I have the frp server in a kubernetes cluster behind an ingress.
If I just expose frps trough tcp routing with sni '*', then frpc connects just fine.
But we need several frp instances in our cluster and want to do routing based on sni name, which requires tls.
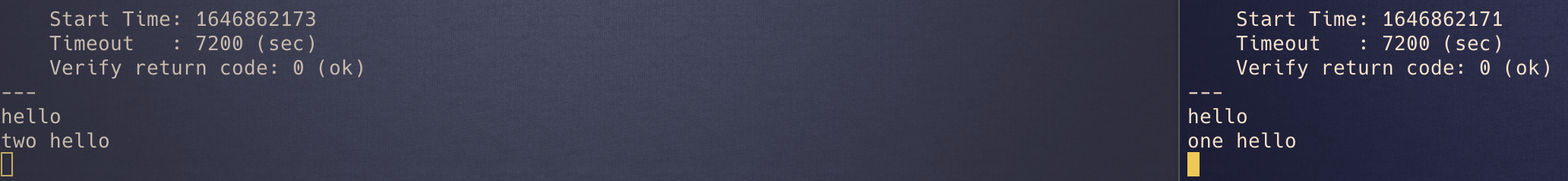
So I got a certificates for a couple of subdomains from lets encrypt and tested with two tcp-echo containers, that got hosted on their own certificate and sni. Connecting with
and
that both go through the same LB into the same ingress works as expected. I can type messages and get them echoed.
But when I try to expose frps over tls things stop working.
The ingress terminates tls, and forwards the traffic to frps on binding port 80.
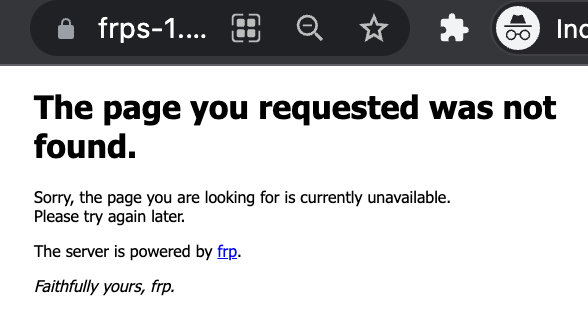
Even though I can still see the frp 404 screen if I use https in address, instead of http, like so - https://frps-1.mydomain.com:32000
frpc refuses to connect.
Openssl still reports perfectly fine tls certificate from lets encrypt...
Any ideas what needs to be configured or fixed to connect over tls with certificate termination in ingress?
frpc Version
0.39.1
frps Version
0.39.1
System Architecture
server: linux/amd64, client: apple silicon
Configurations
frps.ini
frpc.ini
Logs
Even I run frps with
log_level = traceI hardly get any useful logs....Steps to reproduce
Affected area
@fatedier commented on GitHub (Mar 10, 2022):
Try to add
disable_custom_tls_first_byte = trueinfrpc.ini?@presidenten commented on GitHub (Mar 10, 2022):
@fatedier
I tried it already, by tested again.
I could setup an environment in kubernetes for you to test it out if it would help?
Or if you have anything else I could try, Im all ears!
@fatedier commented on GitHub (Mar 10, 2022):
It's not https protocol between frpc and frps. I'm not sure if it can work in this way.
You can provide your ingress yaml.
@presidenten commented on GitHub (Mar 10, 2022):
Sure.
First install emissary according to official instructions: https://www.getambassador.io/docs/emissary/latest/topics/install/helm/
But with overrides on available ports.
filename
tcp.yamlThen install emissary ingress
create a tcp tls listener in namespace emissary, the protocol needs to be set to TCP if you want to test without tls
then in your working namespace apply the following:
If you are testing with listener with protocol TCP, just remove the .spec.host from the TCPMapping
For testing purposes you can just use nip.io, where your domain would be
frps-1-2-3-4.nip.ioif your public ip was 1.2.3.4.@fatedier commented on GitHub (Mar 10, 2022):
Oh,it's not ingress-nginx.
I have not enough time to learn a new ingress implementation. Hope others can help you~
@presidenten commented on GitHub (Mar 10, 2022):
@fatedier What if I create a cluster for you with everything preconfigured?
Normal ingress-nginx cant handle tcp routing with sni because its level 7
@presidenten commented on GitHub (Mar 10, 2022):
@fatedier
It would be in our aws infra ofc. But Ill fix certificates, set it up with domain names, make sure echo servers are in place so you can verify sni routing is working etc.
Then you can just focus on the frp part?
@fatedier commented on GitHub (Mar 10, 2022):
@bingtianbaihua Do you have time to track this issue?
@presidenten commented on GitHub (Mar 10, 2022):
I have an new, and otherwise empty dev cluster, prepared if you guys would be interested to test?
Its on its own vpc and not connected to anything else, so no risk of ruining anything.
@presidenten commented on GitHub (Mar 10, 2022):
I solved it.
PR coming soon.