mirror of
https://github.com/netblue30/firejail.git
synced 2026-05-15 14:16:14 -06:00
[GH-ISSUE #4965] The latest stable chrome (98.0.4758.102) does not start with firejail. #2840
Labels
No labels
LTS merge
LTS merge
bug
bug
converted-to-discussion
doc-todo
documentation
duplicate
enhancement
file-transfer
firecfg
firejail-in-firejail
firetools
graphics
help wanted
information_old
installation
invalid
modif
moved
needinfo
networking
notabug
notourbug
old-version
overlayfs
packaging
profile-request
pull-request
question
question_old
removal
runtime-permissions
sandbox-ipc
security
stale
wiki
wiki
wontfix
wordpress
workaround
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference: github-starred/firejail#2840
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @reagentoo on GitHub (Feb 20, 2022).
Original GitHub issue: https://github.com/netblue30/firejail/issues/4965
Description
Latest stable chrome (98.0.4758.102) does not start with firejail.
Steps to Reproduce
Steps to reproduce the behavior
Expected behavior
Open browser.
Actual behavior
Browser does not start.
Behavior without a profile
Browser works without a profile.
Environment
Linux Gentoo ~amd64
firejail version 0.9.68
chrome 98.0.4758.102
Checklist
/usr/bin/vlc) "fixes" it).https://github.com/netblue30/firejail/issues/1139)browser-allow-drm yes/browser-disable-u2f noinfirejail.configto allow DRM/U2F in browsers.--profile=PROFILENAMEto set the right profile. (Only relevant for AppImages)Log
Output of
LC_ALL=C firejail --debug google-chrome-stable -ozone-platform=waylandhttps://gist.github.com/reagentoo/b93887dde23d149b945b6e9c97760e20
@rusty-snake commented on GitHub (Feb 20, 2022):
Duplicate of #4961/#4960 I guess.edit: no, duplicate of #4929.Does
firejail --ignore=nogroups /usr/bin/google-chrome-stable --ozone-platform=waylandwork?@reagentoo commented on GitHub (Feb 20, 2022):
Does not work.
@rusty-snake commented on GitHub (Feb 20, 2022):
Can you post
/etc/firejail/chromium-common.profile.@reagentoo commented on GitHub (Feb 20, 2022):
Output of
cat /etc/firejail/chromium-common.profile@rusty-snake commented on GitHub (Feb 20, 2022):
but it ever
Found whitelist-usr-share-common.inc profile in /etc/firejail directory Reading profile /etc/firejail/whitelist--usr-share-common.incin the log or processing it.@reagentoo commented on GitHub (Feb 20, 2022):
/etc/firejail/whitelist-usr-share-common.incexists, but it's really missing in the logs..@rusty-snake commented on GitHub (Feb 20, 2022):
Because it's google-chrome and not chromium.
@rusty-snake commented on GitHub (Feb 20, 2022):
Duplicate of #4929
@rusty-snake commented on GitHub (Feb 20, 2022):
See https://github.com/netblue30/firejail/issues/4929#issuecomment-1036032104
@reagentoo commented on GitHub (Feb 20, 2022):
Thanks!
it has resolved the problem
@jose1711 commented on GitHub (Mar 4, 2022):
I have a similar problem. Arch Linux,
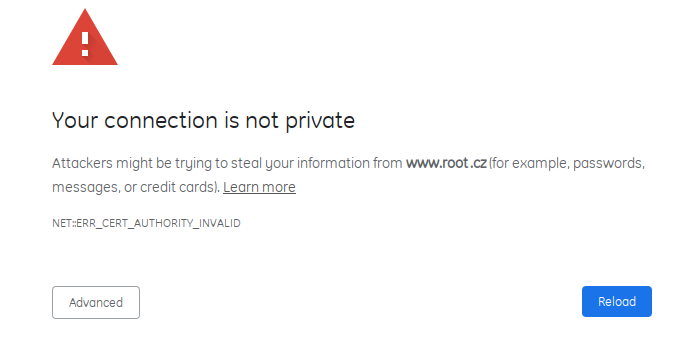
google-chrome 99.0.4844.51-1,firejail11af029. For me however the browser starts, I am able to select user profile, even loading pages but only those which use http:// protocol. For https:// I am getting:This is what appears in the console:
Removing lines
From
chromium-common.profilefixes the problem.@ghost commented on GitHub (Mar 4, 2022):
@jose1711 Nice to see you've found a fix. Those two lines moved from chromium.profile to chromium-common.profile in
0319fbdc4b. Not sure why, but @reinerh probably had good reasons to do so. Let's see if we can come up with a better compromise somehow.@reinerh commented on GitHub (Mar 4, 2022):
See discussion in the PR #4828.
(other chromium-based browser also support webwext extensions)
@ghost commented on GitHub (Mar 4, 2022):
@reinerh Ah, now I remember, thanks for the link to the discussion. Just a thought, would adding:
to our google-chrome-* profiles interfer with Debian bug https://bugs.debian.org/1003234? If not it might be the best of both worlds :-)
@rusty-snake commented on GitHub (Mar 4, 2022):
Still in my todo: https://github.com/netblue30/firejail/issues/4929#issuecomment-1036032104 (opera should be fine with #4999).
If someone else is faster, go for it.