mirror of
https://github.com/netblue30/firejail.git
synced 2026-05-15 14:16:14 -06:00
[GH-ISSUE #2799] --overlay-named exits with error as of linux 5.1.15 (overlayfs) #1753
Labels
No labels
LTS merge
LTS merge
bug
bug
converted-to-discussion
doc-todo
documentation
duplicate
enhancement
file-transfer
firecfg
firejail-in-firejail
firetools
graphics
help wanted
information_old
installation
invalid
modif
moved
needinfo
networking
notabug
notourbug
old-version
overlayfs
packaging
profile-request
pull-request
question
question_old
removal
runtime-permissions
sandbox-ipc
security
stale
wiki
wiki
wontfix
wordpress
workaround
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference: github-starred/firejail#1753
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @lskrejci on GitHub (Jun 26, 2019).
Original GitHub issue: https://github.com/netblue30/firejail/issues/2799
Running
firejail --noprofile --overlay-named=testfails:dmesg on both system configurations contains:
The same command works on linux 5.1.14.
Upstream commit that appears to have introduced the issue: ovl: detect overlapping layers
Environment:
Relates to:
@Hello71 commented on GitHub (Jul 16, 2019):
I think --rbind might be able to work around this.
@Vincent43 commented on GitHub (Sep 7, 2019):
Fix for docker:
477bf1e413@smitsohu commented on GitHub (Sep 18, 2019):
Maybe I don't fully understand the docker fix, but I wonder a bit what's the point of an overlay just to make the file system read-only.
@netblue30 do you have an idea regarding the way forward?
@smitsohu commented on GitHub (Sep 19, 2019):
Or maybe it could serve as a simple switch for apps that really don't need to write anything at all.
@Vincent43 commented on GitHub (Sep 22, 2019):
There is some kernel fix available in Linux 5.3.1 and 5.2.17, @lskrejci could you try if you can still reproduce issue no those kernels?
@Vincent43 commented on GitHub (Sep 22, 2019):
Still fails on Linux 5.2.17 so some firejail changes are still needed:
@schendstok commented on GitHub (Sep 24, 2019):
The same problem happens with the latest Linux kernel update in Debian Buster.
With the previous 4.19.0-5 kernel Firejail works fine with the overlay feature, but when you upgrade to 4.19.0-6 you get the same "fs_overlayfs: Too many levels of symbolic links" error
@Vincent43 commented on GitHub (Sep 24, 2019):
I guess debian backported upstream patches as they were security related.
@Hocuri commented on GitHub (Oct 20, 2019):
I have the same problem (at least I think that it's the same) and some logs:
and:
Kernel 4.19.79-1-MANJARO x86_64.
@netblue30 commented on GitHub (Nov 8, 2019):
For now, I ended up disabling --overlay feature for kernels 4.19 and newer.
I am getting "fs_overlayfs: Too many levels of symbolic links" on debian stable, kernel 4.19.
@Hello71 commented on GitHub (Nov 8, 2019):
I recall testing and finding that mount --rbind did fix the issue. I can't quite recall what I bind mounted though.
@Hello71 commented on GitHub (Nov 8, 2019):
I think it's a similar trick to making pivot_root works, you do
mount --rbind $dir $dirand then that "tricks" the kernel into allowing it.@netblue30 commented on GitHub (Nov 13, 2019):
thanks, I'll try it out!
@springzfx commented on GitHub (Dec 17, 2019):
Distribution: Arch Linux
firejail: 0.9.60-1
linux: 5.4.3.arch1-1
still have the same problem.
@rusty-snake commented on GitHub (Dec 17, 2019):
@springzfx OP use the same firejail version. There is a release coming, see release-0.9.62 branch.
@springzfx commented on GitHub (Dec 17, 2019):
Distribution: Arch Linux
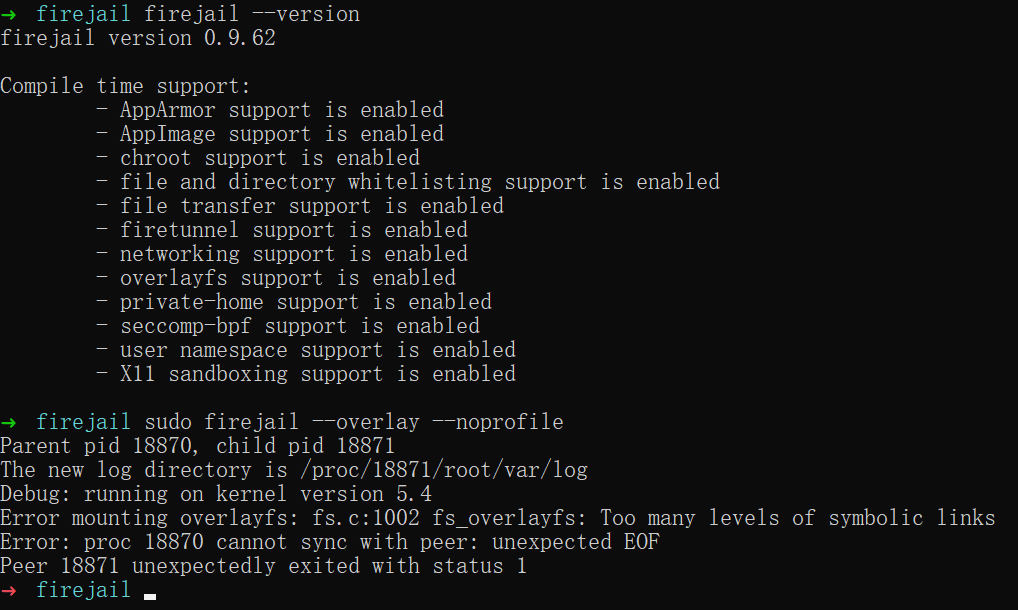
firejail: 0.9.62
linux: 5.4.3.arch1-1
No luck.
@darkf commented on GitHub (Feb 8, 2020):
This still happens, any fixes in sight? Any viable workaround?
@jonleivent commented on GitHub (Mar 8, 2020):
Instead of waiting for kernel fixes related to this, could it be worked around by having firejail use:
https://github.com/containers/fuse-overlayfs
@0x0D15 commented on GitHub (Mar 19, 2020):
@netblue30 Is there any planned fix or known workaround for this issue? It was one of my favorite things about this project.
@Hello71 commented on GitHub (Apr 2, 2020):
took another look at the issue. I think the kernel is valid to reject this mount. if you do
firejail --overlay-named=xand then access$HOME/.firejail/xthen there would be a cycle. but, that change also added runtime checking, so you can apply a patch like this:then, patch firejail to use
mount -o ignore_overlap=on.@firejailing commented on GitHub (Aug 12, 2020):
@netblue30 where are you?
this has been broken for over a year now, ridiculous, new profiles are less important than fixing this
@shuhaowu commented on GitHub (Aug 21, 2020):
Are there no workarounds for this for now?
@reinerh commented on GitHub (Oct 3, 2020):
Another workaround has been suggested in: https://bugs.debian.org/971578
@garywill commented on GitHub (Dec 30, 2020):
--overlayused to work for me in May 2019 (on openSUSE 15.0 or 15.1).But not now. Now I'm on openSUSE 15.2 with kernel 5.3.18
Wish a fix. Thanks all developers 👍 :)
@pushqrdx commented on GitHub (Apr 11, 2021):
same here
@Ristovski commented on GitHub (Jul 11, 2022):
@netblue30 Any news on this? I too like the suggested alternative of using
fuse-overlayfswhich is also whatpodmanuses for example.@rusty-snake commented on GitHub (Jan 28, 2025):
https://github.com/netblue30/firejail/pull/6632#discussion_r1929573432:
@kmk3 commented on GitHub (Dec 19, 2025):
Closing, as overlayfs support was removed: